Co-Managed IT vs Fully Managed IT: When Each Model Wins
Choosing the right IT operating model is about risk, accountability, and execution — not preference or budget alone.
- Designed for regulated and operationally mature organizations
- Clear responsibility boundaries and execution ownership
- Supports both internal IT teams and full outsourcing models
- Built for auditability, uptime, and cyber insurance alignment
35+
Years of Proven Expertise
15+
Industries Served
10,000+
Alerts Handled, Zero Missed
98%
Client Retention Year After Year
35+
Years of Proven Expertise
15+
Industries Served
10,000+
Alerts Handled, Zero Missed
98%
Client Retention Year After Year
Why the IT Operating Model Matters More Than Ever
Organizations no longer choose IT models based solely on cost. Cyber insurance requirements, compliance obligations, uptime expectations, and internal staffing realities now dictate whether co-managed or fully managed IT is the correct approach.
The decision impacts every aspect of your technology operations, from day-to-day incident response to long-term strategic planning. Getting it wrong creates technical debt, operational friction, and exposure that compounds over time.
Choosing the wrong model often leads to:
- Tool sprawl with no execution
- Gaps in accountability during incidents
- Audit and insurance exposure
- Burnout of internal IT teams
The right model aligns technical capabilities with business risk tolerance, regulatory requirements, and operational maturity.
It establishes clear ownership boundaries while maintaining the flexibility to evolve as your organization grows.

Cyber Risk
Insurance requirements and threat landscape demand proven execution capability

Compliance Pressure
Regulatory frameworks require documented controls and continuous monitoring

Operational Uptime
Business continuity depends on 24/7 monitoring and rapid incident response

Accountability
Clear ownership prevents gaps during critical incidents and audits
Co-Managed IT Is the Right Fit When:
The co-managed model works best for organizations that have existing IT capabilities but need specialized execution support, enhanced security operations, or compliance program delivery. It’s designed for teams that want to retain strategic control while offloading operational burden.
You Have Capable IT Staff
Your internal team has the expertise and institutional knowledge to manage business systems, but they lack a dedicated SOC or compliance team to handle the security and regulatory execution layer.
Security and Uptime Must Improve
Current security posture or operational uptime doesn’t meet business, insurance, or regulatory requirements — and improving them requires specialized tools, processes, and 24/7 staffing you don’t have in-house.
Tools Exist But Aren't Fully Leveraged
You’ve invested in security tools,
monitoring platforms, or compliance systems, but they’re underused or misconfigured. You need execution expertise, not more technology.
Audit or Insurer Requirements Demand Proof
Cyber insurance applications, customer audits, or regulatory examinations require documented controls and continuous monitoring evidence that your current approach can’t consistently deliver.
You Want Flexibility Without Loss of Control
Comprehensive testing and validation ensuring coverage, performance, and security meet design specifications before handoff.
A Common Path: Co-Managed Today, Fully Managed Tomorrow
Many organizations begin with co-managed IT to stabilize operations, reduce risk, and prove the partnership model. As complexity grows, internal priorities shift, or risk tolerance decreases, they transition seamlessly to fully managed IT — without changing providers, rebuilding documentation, or re-establishing trust

Stabilize Operations
Begin with co-managed execution to fill security, monitoring, and compliance gaps while preserving internal IT ownership and strategic control.

Reduce Risk & Document Controls
Establish documented controls, continuous monitoring, and audit ready evidence. Build confidence in the partnership and execution model.

Offload More Responsibility
As complexity grows or priorities shift, transfer additional operational layers to BTI — helpdesk, project delivery, vendor management, change control.

Transition to Fully Managed
Move seamlessly to fully managed IT when centralized accountability, reduced overhead, or strategic focus become business priorities.
BTI supports both models — so transitions do not require changing providers, rebuilding trust, or re-documenting your environment. We scale with you. This progression avoids re-platforming, re-auditing, or re-education of a new provider
Co-Managed IT Is the Right Fit When:
You Have Capable IT Staff
Security and Uptime Must Improve
Tools Exist But Aren't Fully Leveraged
Audit or Insurer Requirements Demand Proof
You Want Flexibility Without Loss of Control
Fully Managed IT Is the Right Fit When:
Accountability Must Be Centralized
Internal IT Bandwidth Is Constrained
Uptime and Security Risk Tolerance Is Low
Regulatory and Insurance Exposure Is High
Leadership Wants Predictable Outcomes
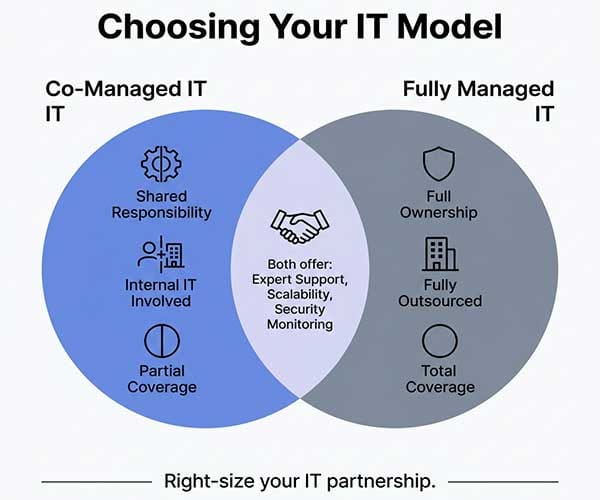
Co-Managed IT vs Fully Managed IT At a Glance
Understanding the operational and accountability differences between these models is essential for making the right choice for your organization. The table below breaks down key capabilities and ownership structures.
| Capability | Co-Managed IT | Fully Managed IT |
|---|---|---|
| Internal IT Team | Required | Optional |
| Day-to-Day Execution | Shared | BTI Owned |
| NOC / SOC / SIEM | Included | Included |
| Compliance Execution | Included | Included |
| User Helpdesk | Shared | BTI Owned |
| Project Delivery | Shared | BTI Owned |
| Accountability Model | Documented SRM | Single Owner |
| Best For | Operationally mature teams | Organizations needing full ownership |
Both models include BTI’s reporting, PSA, SOC, SIEM, MDR, and compliance execution layers. The distinction is where operational ownership and escalation authority reside.
Why Organizations Trust BTI With Either Model
Whether you choose co-managed or fully managed IT, you need a provider with proven operational maturity, security expertise, and the certifications to back it up. BTI delivers infrastructure-led operations with integrated cybersecurity and compliance execution.
Compliance Certifications
BTI Certifications


Certifications via Third-Party Data Centers & Service Providers










BTI Certifications


Certifications via Third-Party Data Centers & Service Providers










Related IT Services
Related Articles
Key Takeaways ✔ Co-managed IT reduces internal IT burnout by shifting operational execution to
Most IT organizations do not fail because they lack technology. They fail because their
Many organizations believe they are running a hybrid IT model some internal staff, some
Most audit failures do not happen because organizations lack security tools. They happen because
Operating in a Converged IT + Security + Voice Environment?
We’ll help you:
- Assess cross-system dependencies that create outages and security gaps
- Identify governance issues caused by fragmented tools and vendors
- Determine whether BTI can standardize and support your environment long-term











