Kantech, ExacqVision, DSC: Johnson Controls’ Manufacturing Division’s Budget-Friendly, Cyber-Hardened, Open AI-Ready Security Solution (2026)
Choosing a security platform in 2026 is no longer just about features—it’s about control, cost structure, cybersecurity, and long-term flexibility.
Organizations today are evaluating two fundamentally different approaches:
Cloud security system platforms that prioritize simplicity and centralized management
Open architectures that prioritize control, adaptability, and long-term cost stability
Kantech, ExacqVision, DSC, and Alarm.com—especially when paired with Axis cameras—represent one of the most widely deployed open, non-proprietary security architectures available.
At BTI Communications Group, our role is not to push one model over another. It is to help organizations understand the trade-offs, design the right system, and implement it correctly—based on their environment, resources, and long-term goals.
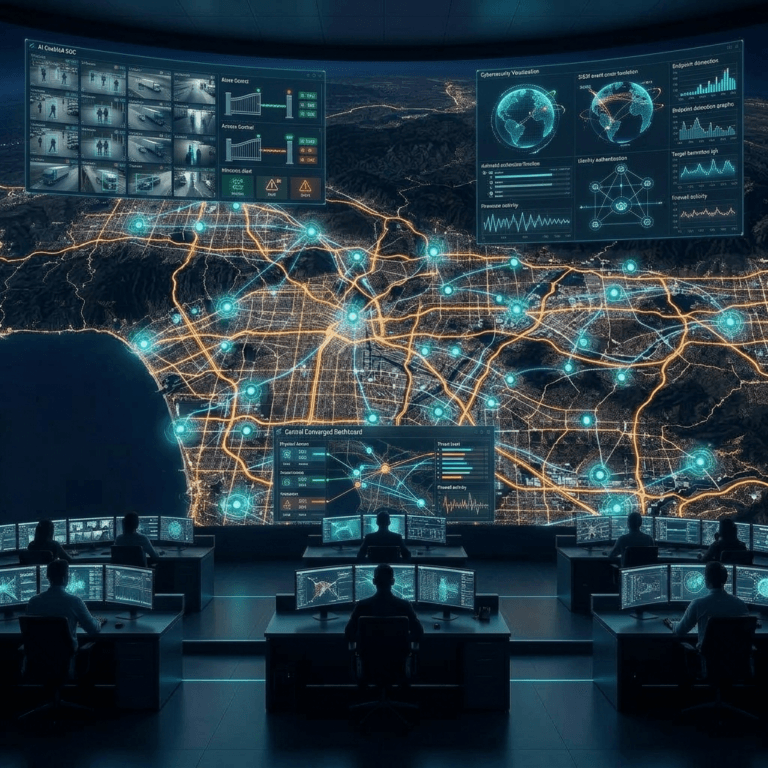
ISC West 2026 Confirmed It: Flexibility and AI Readiness Are Driving Security Strategy
At ISC West 2026, the direction of the market became clear:
Cybersecurity, identity, and data control are becoming central to system design
Converged Physical and Cybersecurity Governance is Now Table Stakes for Compliance
As a result, many organizations are reassessing how much control they want over their systems—and how they plan to evolve them over time.
There Is No Single “Best” System—Only the Right Fit
One of the most important truths in modern security design is this:
There is no universally “best” platform—only the platform that best aligns with your organization.
Open architectures like Kantech, ExacqVision, DSC, and Axis are often well suited for organizations that:
Require control over infrastructure and data
Operate in regulated or compliance-driven environments
Need flexibility to integrate with IT and identity systems
Want the ability to adopt AI and analytics from multiple sources
Prefer to avoid long-term vendor lock-in
Cloud platforms are often a strong fit for organizations that:
Prioritize simplicity and speed of deployment
Have limited internal IT or security resources
Prefer subscription-based models
Want minimal involvement in system management
The decision is not technical—it is strategic and operational.
The Operational Reality: Expertise Is Required Either Way
A common misconception is that cloud platforms eliminate complexity.
In reality, both open and cloud systems require:
Professional design and system architecture
Network and infrastructure readiness
Proper configuration of devices, users, and policies
Ongoing management, updates, and optimization
- Rigorous Identity Access Control
The difference is not whether expertise is required—it is how systems are managed and who controls them over time.
For organizations with lean IT teams, managing open systems internally can become challenging without the right partner.
This is where BTI provides value—not just in deployment, but in ongoing support, optimization, cybersecurity alignment, and converged security management.
A More Realistic Cost and Control Comparison
The difference between open and cloud systems is often oversimplified.
The reality is more nuanced.
Cloud Platforms: Simplicity with Dependency
Cloud systems provide:
Centralized management
Streamlined updates and maintenance
Reduced on-premise infrastructure
But they also introduce:
Ongoing subscription dependency
Loss of functionality if licensing lapses
Limited data ownership and governance
Vendor-controlled upgrade paths and pricing
Costs that scale continuously with device count
For smaller, non-regulated environments, these trade-offs are often acceptable.
At scale, they become more impactful.
Open Architecture: Control, Flexibility, and Cost Stability
Open systems like Kantech, ExacqVision, DSC, and Axis shift the model:
Systems are owned, not rented
Licensing is typically perpetual rather than subscription-based
Infrastructure and data remain under organizational control
Upgrades and enhancements can be implemented on your timeline
This enables:
Deferred maintenance flexibility without system shutdown
Data ownership and governance aligned to compliance requirements
Flexible upgrade paths without full system replacement
Freedom to adopt AI and analytics tools independently
Where the Difference Becomes Significant
In smaller deployments, cost differences may be modest.
In larger or regulated environments, the gap becomes more pronounced due to:
Device count (cameras, doors, sensors)
Retention requirements for video and data
Cybersecurity and monitoring requirements
Compliance and audit obligations
Data storage and governance controls
In 2026, organizations often find:
Cloud costs scale continuously and predictably upward
Open systems require more upfront planning but stabilize over time
Infrastructure reuse and phased upgrades significantly reduce lifecycle cost
In addition:
Open systems allow organizations to control when and how costs are incurred, rather than being locked into ongoing subscription models.
Legacy Infrastructure Reuse: A Cost and Timing Advantage
One of the most practical advantages of this architecture is the ability to reuse existing infrastructure speeding deployment and driving down cost.
Organizations can:
Retain existing sensors, devices, cabling and network infrastructure investments
Reuse compatible cameras and access hardware
Upgrade systems in phases
Avoid full rip-and-replace deployments
This enables a controlled modernization strategy, reducing:
Capital expenditure
Deployment disruption
Operational risk
Cyber Hardenability and Regulatory Alignment
Open architectures are particularly popular in regulated and security-sensitive environments.
They allow organizations to:
Define and enforce their own cybersecurity policies
Control network segmentation and device access
Align systems with compliance frameworks
Maintain full control over data storage and governance
This is critical in industries such as:
Where control is not optional—it is required.
Axis Cameras + ExacqVision 26: Open Video, AI, and Identity
At the core of this architecture is a highly flexible video platform.
ExacqVision 26 expands beyond traditional video management into a video, integration, and identity-aware platform.
When paired with Axis cameras—recognized globally for advanced imaging and edge AI—the result is a powerful and adaptable system.
Together, they provide:
High-performance, cyber-secure video infrastructure
Native support for virtually all major camera platforms
Edge AI processing directly on the camera
Integration with server-based and third-party analytics
Expanded identity and access system alignment including Entra ID and HID’s new Converged Credentials
Improved cybersecurity and system resilience
ExacqVision 26 also enhances:
Alignment between video, user activity, and access events
Hybrid deployment flexibility
Scalability across multi-site environments
This allows organizations to deploy:
Advanced detection and classification models
Behavioral and anomaly analytics
AI-driven monitoring and automation
Custom analytics tailored to their environment
For complex and multi-threaded AI application uses, open systems ensure freedom to adopt new AI technologies without replacing their core systems entirely.
Kantech (Latest EntraPass): Access Control with Identity Flexibility
Kantech’s latest EntraPass platform provides a flexible and scalable access control foundation.
It enables:
Multi-site deployment and centralized management
Integration with video, intrusion, and identity systems
Support for evolving credential strategies
Alignment with enterprise identity environments
Organizations can:
Integrate with existing identity databases
Customize workflows and credential strategies
Adapt to mobile and converged identity models
This flexibility is critical for organizations that require identity integration without vendor lock-in.
DSC + Alarm.com: Reliable Detection and Visibility
DSC and Alarm.com provide a dependable intrusion and alerting layer.
They deliver:
Proven detection capabilities
Real-time alerts and notifications
Remote visibility and system access
- Ability to deploy cloud- based applications tied to intrusion panels with built-in off network cellular connectivity
While intentionally simple in integration, they provide:
Immediate awareness of events
Operational reliability
A flexible cloud-connected monitoring layer with redundant, network and/or cellular connectivity
AI and Automation: A Platform That Evolves Over Time
One of the strongest advantages of this architecture is its ability to evolve.
Because it is open:
Third-party AI platforms can be integrated
Custom automation workflows can be developed
New technologies can be adopted without replacing infrastructure
This creates a system that improves over time rather than becoming obsolete. In fact, at BTI, we have clients that have been updating Kantech, DSC, and ExacqVision without replacing hardware devices for over a decade. With infrequent updates to servers and firmware and addition of open AI applications, these systems can be perpetually “state of the art.”
BTI’s Approach: Transparent Design, No Commitment, Full Visibility
Selecting the right security architecture requires more than product knowledge—it requires clarity and transparency.
BTI provides:
No-commitment system design and consultation
Fully itemized scope, architecture, and budget breakdowns
Evaluation of all viable deployment options
Planning for:
Ongoing proactive maintenance, support, and optimization services
Our role is to help you understand what is possible, what it costs, and what aligns best with your organization—before any decisions are made.
Final Takeaway: The Right Architecture Is the One That Fits Your Strategy
In 2026, the most effective security systems are not defined by a single vendor or model.
They are defined by how well they align with:
Your operational capabilities
Your cybersecurity requirements
Your compliance obligations
Your long-term strategy
Open architectures offer control, flexibility, and adaptability.
Cloud platforms offer simplicity and centralization.
The right choice depends on your organization—not the technology.
Next Step
If you are evaluating security systems and want a clear, unbiased understanding of your options, BTI can help you:
Compare open vs cloud architectures
Evaluate cost, risk, and scalability
Design a system aligned with your business and IT strategy
Ready to Evaluate the Right Security Approach for Your Organization?
Contact BTI Communications Group to design a security strategy that aligns with your infrastructure, goals, and future.