Key Takeaways
- Growth increases network complexity faster than most teams can manage. As organizations expand across locations, cloud platforms, remote users, and connected devices, the network becomes harder to monitor and control.
- Unmanaged devices and fragmented networks create visibility gaps. When employees access systems from unmanaged devices and multiple networks, traditional security and monitoring approaches struggle to keep pace.
- Visibility is the foundation of both networking and cybersecurity. If IT teams cannot see the full path from user → device → network → cloud application, they cannot reliably secure or support the environment.
- Operational discipline matters more than adding more tools. Organizations benefit most from unified monitoring, standardized controls, and consistent governance.
- BTI GlobalView restores visibility and control. GlobalView provides centralized monitoring, AI-assisted threat detection, and engineering-backed support to help organizations maintain secure, reliable operations as they scale.
Business growth is a win, but it comes with a hidden cost: network complexity.
As organizations add locations, cloud workloads, remote users, IoT devices, and hybrid work patterns, visibility becomes harder, and IT teams get stretched thin. That’s when risk shows up first as “small issues” (slowdowns, outages, inconsistent access), and later as security gaps, downtime, and audit pressure.
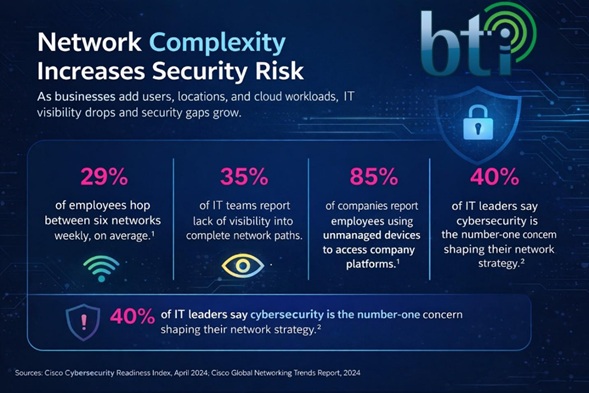
Cisco research quantifies what many IT leaders are experiencing:
- 85% of organizations say employees access company platforms from unmanaged devices.
- 29% report employees hop between at least six networks weekly.
- 40% of IT leaders cite cybersecurity as the number one concern impacting networking strategy.
The takeaway is not “buy more tools.” The takeaway is this: you need a unified strategy that turns complexity into control.
BTI GlobalView support and our co-managed IT and security model are built to do exactly that, delivering control, visibility, and protection across environments, without vendor sprawl.
What’s happening: growth increases network complexity faster than most teams can manage.
Why it matters: unmanaged devices + limited visibility increase downtime and breach risk.
What to do: standardize secure networking, reduce blind spots, and operationalize monitoring and response.
How BTI helps: GlobalView delivers unified visibility, AI-assisted monitoring, and engineering-backed remediation across IT, cybersecurity, and converged physical security.
Why Network Complexity Creates Risk
The modern environment is no longer one network
Most organizations now operate across:
- office networks and warehouse networks
- multiple ISPs and SD-WAN links
- cloud platforms and SaaS applications
- unmanaged devices, guest devices, and IoT endpoints
- remote users moving across home, mobile, and public networks
That’s why “visibility” is now a business requirement. If you cannot see the path from user → network → cloud app → identity → endpoint, you cannot reliably secure it or support it.
The Two Problems Cisco’s Stats Highlight
1) Unmanaged devices are normal, and they change the threat model
When employees access corporate platforms from unmanaged devices, you lose:
- consistent endpoint security controls
- consistent patch compliance
- reliable device identity and posture
- predictable access governance
This is exactly why identity-based security and layered controls matter. Unmanaged devices are not a niche edge case; they are part of the operating reality.
2) Visibility breaks first, then downtime and security gaps follow
As complexity grows, IT teams often lose visibility into:
- end-to-end network paths
- policy enforcement consistency
- performance root cause
- “shadow” access methods and exceptions
The result is an environment that functions until it doesn’t. That’s when response becomes reactive, expensive, and disruptive.
What “Secure Networking and Assurance” Looks Like in Practice
BTI’s approach is infrastructure-led: we start with the network because the network is the foundation for cloud access, security, VoIP, physical security systems, and business continuity.
A mature, secure networking posture includes:
1) Control
- segmented networks (business systems, IoT, guest, security devices)
- enforced access policies
- hardened remote access pathways
2) Visibility
- unified monitoring across WAN, LAN, Wi-Fi, cloud paths, and endpoints
- actionable alerting that reduces noise
- reporting that leadership can use (risk + uptime + compliance readiness)
3) Protection
- firewall governance and threat prevention
- endpoint/XDR coverage
- vulnerability and patch governance
- identity hardening and least privilege
Outcome: fewer blind spots, faster resolution, and a security posture you can prove under audit or insurance scrutiny.
Where BTI GlobalView Fits
BTI GlobalView is designed to help mid-market organizations stay agile without losing control.
It provides:
- centralized visibility across infrastructure and security layers
- AI-assisted monitoring and threat prevention
- remote and on-site engineering support
- operational routines that keep controls enforced (patching, lifecycle, governance)
This is how we reduce “tool sprawl” and replace it with operational discipline.
Why This Matters for Multi-Site Organizations
For multi-site operations, the risk compounds:
- more networks, more devices, more exceptions
- inconsistent user experience across locations
- higher downtime cost
- broader compliance and insurance exposure
BTI supports organizations across Los Angeles, Orange County, Chicago, and Phoenix with a model that combines centralized operations with local engineering execution.
What BTI Protects (Converged by Design)
BTI converged security services protects people, assets, and devices across the full environment, including:
- firewalls and network infrastructure
- endpoint protection and XDR
- access-controlled doors and visitor management
- cameras and alarm monitoring
- VoIP and AI-enabled contact center services
The differentiator is integration. These systems should not be secured in silos; they must be operated as one environment.
Practical Next Step: A Visibility and Risk Review
If your organization is scaling and your team is stretched thin, the next best step is not another tool. It’s a structured review:
- Where are unmanaged devices touching corporate platforms?
- Where are network paths and policies not visible from end-to-end?
- Are security and physical systems running on the same infrastructure without segmentation?
- Can you prove that controls are enforced (not just “installed”)?
Request a Network Visibility and Risk Review
BTI will evaluate your environment, identify where visibility breaks down, and provide a roadmap to strengthen networking, security, and operational monitoring.








