Ontario CA Arson: What the Kimberly-Clark Fire Reveals About Business Risk and Insurance Exposure
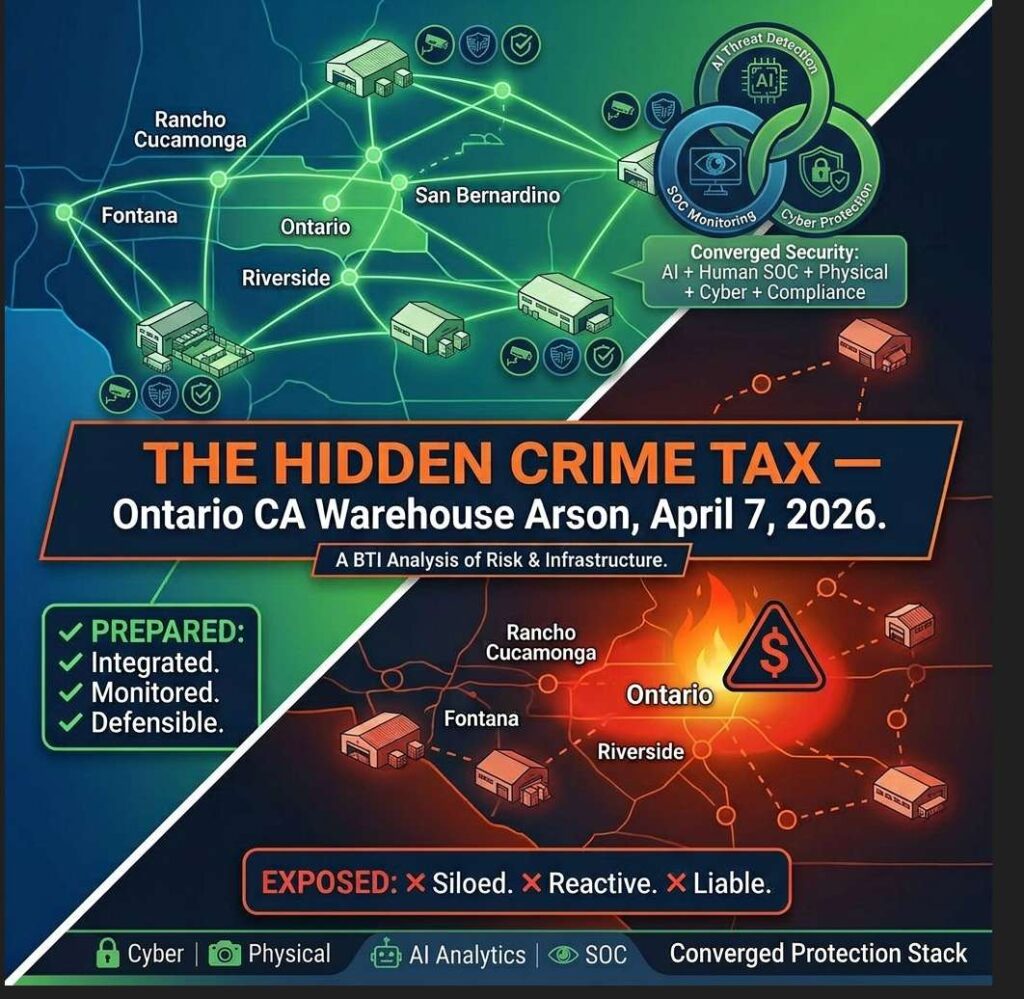
The Rising Cost of Risk: What the Ontario Kimberly-Clark Warehouse Arson Reveals About the Hidden Crime Tax on Inland Empire Businesses Introduction: It’s Not About Prevention—It’s About Preparedness The April 7, 2026 arson at the Kimberly-Clark distribution center in Ontario, California wasn’t random. An employee of third-party operator NFI Industries allegedly live-streamed himself igniting pallets […]
Co-Managed IT vs Fully Managed IT: When Each Model Works and When It Fails

Choosing between co-managed IT and fully managed IT is not about preference or maturity. It is about organizational reality, execution risk, and accountability. Many organizations choose the wrong model — not because they lack tools or intent, but because they misunderstand what each model is designed to do. This guide explains: What co-managed IT actually […]
Axis Camera Installation & Design: Work with a Certified Axis Gold Partner for Secure, AI-Driven Systems

Axis Camera Installation & Design: Work with a Certified Axis Gold Partner for Secure, AI-Driven Systems In the world of enterprise security, anyone can sell you a box. But in 2026, that box is no longer just a camera—it’s an intelligent sensor, a cybersecurity endpoint, and a node in your identity and operational infrastructure. As […]
HID Converged Credentials: Unified Zero Trust Security for Physical and Logical Access

HID Converged Credentials Announced at ISC West 2026 HID unveiled a major innovation reshaping enterprise security: HID’s 2026 State of Security and Identity Report describes 7 key trends that led to the development of their identity solution bridging physical access, IT systems, and cloud environment security. HID’s FIDO2 (passwordless/phishing-resistant), PKI, and OATH capabilities in Crescendo® […]
ISC West 2026 Confirms the Future: Why Converged Security & Co-Managed IT Are Now Essential for Businesses

ISC West 2026 Overview Dates: March 25–27, 2026 Location: Venetian Expo, Las Vegas, Nevada Exhibit Hall: Open throughout the three-day event Conference Program: Runs alongside the event with curated sessions and industry discussions What to Expect: Expert-led education sessions and technical briefings Keynotes and industry panel discussions New product showcases and innovation awards Networking opportunities […]
Operational Reliability in Co-Managed IT: Why Execution Models Matter More Than Tools

When organizations experience outages, security incidents, or audit failures, the root cause is rarely a missing tool. It is almost always an execution failure: Alerts generated but not acted on Maintenance deferred due to staffing constraints Security controls implemented but not continuously validated Responsibility unclear when something breaks This is where operational reliability becomes the […]



