How Co-Managed IT Reduces Internal IT Burnout Without Replacing Your Team

Key Takeaways ✔ Co-managed IT reduces internal IT burnout by shifting operational execution to a specialized partner while preserving strategic control. ✔ Security, compliance, and reliability improve when execution is owned, staffed, and accountable. Internal IT burnout is rarely caused by lack of skill or effort. It happens when execution responsibilities scale faster than staffing, […]
The Co-Managed IT Operational Maturity Model

Most IT organizations do not fail because they lack technology. They fail because their operating model never matures at the same pace as increasing complexity, regulatory pressure, and risk. As environments become more security-sensitive, uptime-critical, and audit-driven, the difference between struggling and succeeding is not tools or headcount — it is operational maturity. This article […]
Why “Hybrid IT” Fails — and Co-Managed IT Succeeds in Regulated Environments

Many organizations believe they are running a hybrid IT model some internal staff, some outsourced tools, some third-party security vendors. In reality, most hybrid environments fail for one reason: No one is operationally accountable when something goes wrong. Alerts fire. Tickets pile up. Tools generate dashboards. But outages persist, controls drift, and audits turn into […]
What IT Compliance Auditors and Assessors Want to See in Audits

Most audit failures do not happen because organizations lack security tools. They happen because organizations cannot prove that security controls are operating consistently, by design, and under clear ownership. In regulated and cyber-insured environments, auditors do not evaluate intent, tool lists, or policy statements. They evaluate evidence — and they expect that evidence to exist […]
Tools vs. Controls: Why Buying Security Software Does Not Equal Security

Tools don’t pass audits. Controls do. And controls only exist when they are operating, enforced, and provable. Most organizations believe they have a security problem. In reality, they have a control execution problem. They own the tools. They pay the licenses. They check the boxes. And yet, when auditors, insurers, or customers ask for proof […]
Milestone XProtect AI & Open VMS Platform: Converged Security, Video Analytics & Integration at Scale (2026)
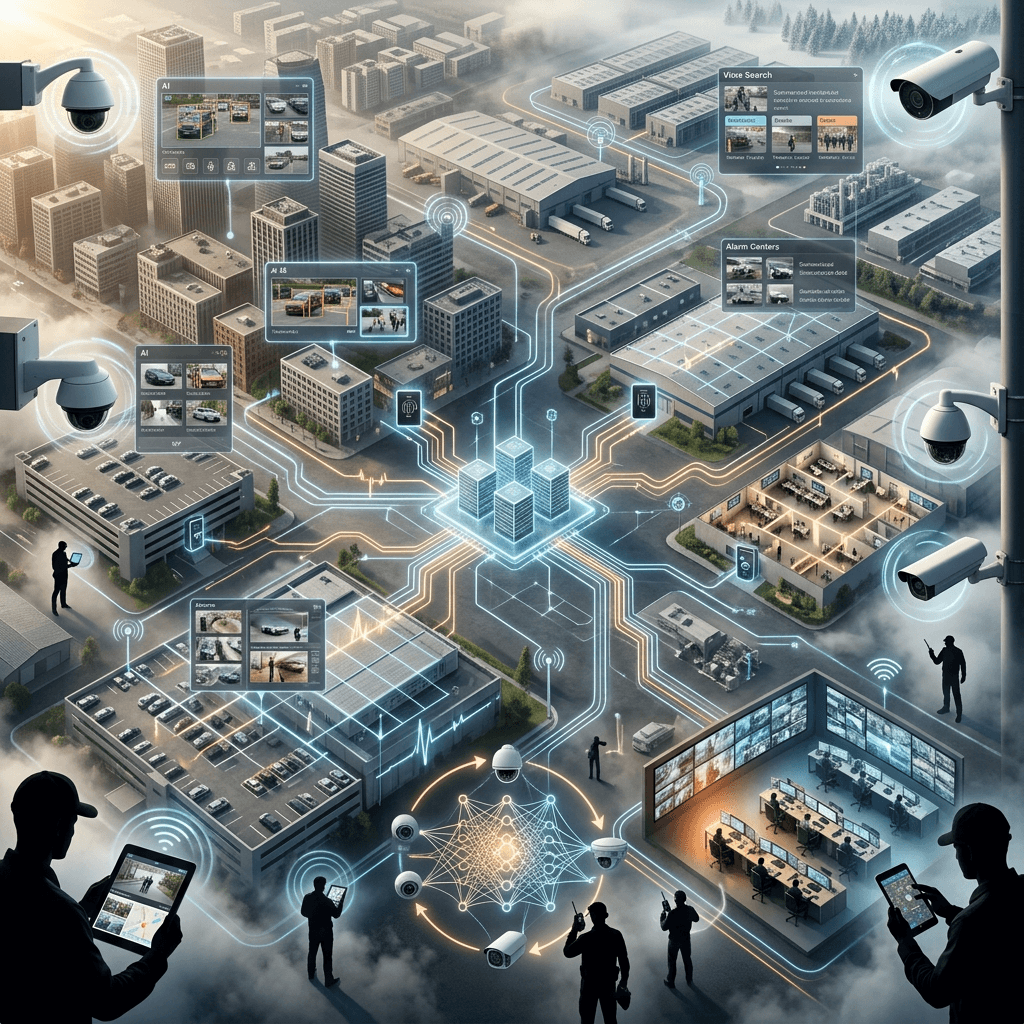
Milestone XProtect & AI at ISC West 2026: The Open Platform for Video, AI, and Converged Security at Scale As security systems evolve, one platform continues to anchor some of the most advanced deployments across enterprise, government, and critical infrastructure environments: Milestone Systems At ISC West 2026, Milestone reinforced its position as the leading open […]



